Agents not compliant with dangerous goods training rules will be struck-off, warns IATA
Forwarder associations are warning members that they must upload their dangerous goods certificates immediately, or ...
TFII: SOLID AS USUALMAERSK: WEAKENINGF: FALLING OFF A CLIFFAAPL: 'BOTTLENECK IN MAINLAND CHINA'AAPL: CHINA TRENDSDHL: GROWTH CAPEXR: ANOTHER SOLID DELIVERYMFT: HERE COMES THE FALLDSV: LOOK AT SCHENKER PERFORMANCEUPS: A WAVE OF DOWNGRADES DSV: BARGAIN BINKNX: EARNINGS OUTODFL: RISING AND FALLING AND THEN RISING
TFII: SOLID AS USUALMAERSK: WEAKENINGF: FALLING OFF A CLIFFAAPL: 'BOTTLENECK IN MAINLAND CHINA'AAPL: CHINA TRENDSDHL: GROWTH CAPEXR: ANOTHER SOLID DELIVERYMFT: HERE COMES THE FALLDSV: LOOK AT SCHENKER PERFORMANCEUPS: A WAVE OF DOWNGRADES DSV: BARGAIN BINKNX: EARNINGS OUTODFL: RISING AND FALLING AND THEN RISING
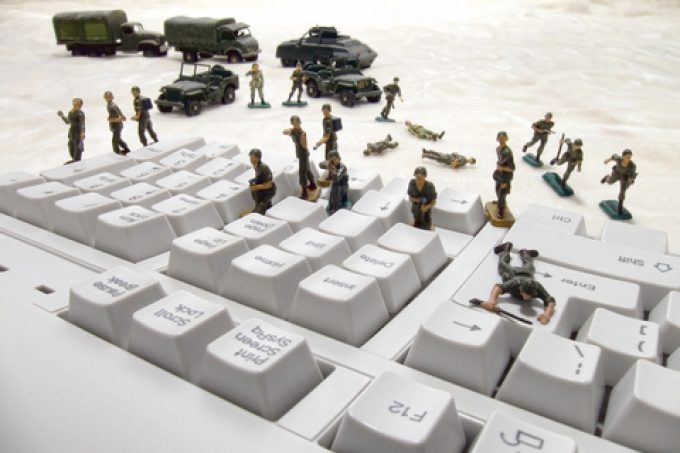
In the week that CMA CGM suffered a data breach, eyes are once again on cyber security.
But while the shipping lines (eg Maersk) and forwarders (ECU Worldwide, Toll Group) have taken the vast majority of headlines, the threat in air cargo is also high.
Between 2019 and 2020, there was a 530% increase in cyber attacks reported to Eurocontrol, while there were 775 cyber attacks on airlines in 2020 – and just 150 at airports.
Some 95% of these attacks were financially motivated, according to the Eurocontol report, leading to a financial loss in 55% of cases. Nearly 35% saw the leaking of data.
Amar More, director at Kale Logistics Solutions, said aviation is a target. “Recently, there has been a clear increase in these attacks and their severity.”
While any attacks on air cargo operations have not been widely publicised, Mr More said they are also at risk.
“More attempts have been made to steal passenger (personal data, credit cards etc) data than cargo. Having said that, a shipment can often involve data or intellectual property transfer between up to 10 separate parties across the globe, hence there is enough motivation for hackers to look at cargo data as well.
“In a nutshell, I would say that both are equally vulnerable to cyberattacks.”
He explained: “In a connected world, a lot of processes of the airlines have moved into an online mode, such as bookings, air waybill data capture, customer service (tracking) etc. Being global entities, airlines get connected with several stakeholders across the globe like travel agents, forwarders, customs, airport systems etc.
“In the cybersecurity world, the chain is as strong as the weakest link. Since the airlines are connected to a lot of smaller entities who do not have the wherewithal to create good cybersecurity infrastructure, there is a constant risk of a cyber attack. In most cases, the hackers are into the system for about eight to nine months, and then they strike when you least expect it. Since the airlines harbour a lot of critical data on passengers and cargo their systems are always at risk.”
While instinctively, it might seem that cargo community systems (CCS) could contribute to cyber security weakness, Mr More said that in fact they enhance protection.
“People who have no cybersecurity capabilities and infrastructure connecting to airlines, customs and airport systems directly, do put these large systems at significant risks.
“However if there is an additional layer of a CCS which typically has seven layers of security, and additional security layers provided by leading cloud providers like Microsoft and Amazon, the cybersecurity risks to the larger stakeholder systems go down significantly.
“I call it democratisation of cyber security. CCS can democratise the cyber security and help provide better security infrastructure to the smaller players and by being a buffer layer with bolstered world-class security infrastructure, reduce the risks for the systems of larger players.
“In short, the community approach to security greatly mitigates these risks. As they say, no one is safe until everyone is safe.
“CCS can lend safety to the ‘not haves’ in the industry. Moreover CCS can also embody other technologies like blockchain to make the supply chain data more secure.”
Another way to lessen the risk is to strengthen vulnerabilities, he added, in people, processes and technology.
“Organisational silos where people do not speak to one another is one weakness hackers can exploit. IATA estimates that more than 70% of hacks begin with interaction between staff and the hacker. So educating employees on these risks is extremely important. Each stakeholder should have at least one resource trained on cybersecurity and there should be a programme in place to educate the others in the organisation.”
In terms of processes, there is an approach.
“Assess – take inventory and frequently audit your IT assets.
“Detect and report – if possible keep a Security Ops Centre (SOC) or some other mechanism to identify and report potential security threats
“Respond – build cyber resilience i.e. have the emergency processes in place in case of cyber attacks
“Learn and Improve – learn from the experiences of yourself and others and continuously improve the cyber security infrastructure.”
Companies can also opt for high-end security tools on software as a service, pay-as-you-go basis. But Mr More warned that risks should be managed at the development stage.
“The new mantra is a framework termed as Dev-Sec-Ops, to handle security issues at the development stage itself before moving potential vulnerable code to production and fixing it later.
“Also, as a first step, every client desktop / laptop should be running with updated operating system patches, anti-virus software always in protected mode and most up-to-date. This will reduce end point vulnerability to a larger extent because 90% of the time attacks are initiated from client desktop / laptops which are compromised.
“Airlines can’t stop all malware from getting in, but they can stop damage to infrastructure and data theft using very secure technology.”
Mr More said the whole industry, not just carriers, “should be worried”, while the bigger the player, the bigger the risk. But that risk should be mitigated in partnership.
“A community approach to cybersecurity is the best thing we can do to mitigate the risks,” he concluded.
Comment on this article